Introduction to Jayde
Jayde is a name that has been associated with various individuals and concepts across different fields, including entertainment, social media, and more. However, without specific context, it’s challenging to pinpoint exactly who or what Jayde refers to in this scenario. For the purpose of this discussion, let’s consider Jayde as a persona or entity that has been involved in leaking information or content, which could range from personal data to creative works.Understanding Leaks
Leaks, in a broad sense, refer to the unauthorized release of information, data, or content. This can happen in various domains, including but not limited to, entertainment, technology, and government. Leaks can have significant consequences, ranging from minor inconveniences to major breaches of privacy or security.5 Possible Ways Jayde Leaked
Considering the vast possibilities of what Jayde could refer to and the nature of leaks, here are five hypothetical ways Jayde might have leaked information or content:- Social Media Mishaps: Jayde might have inadvertently shared confidential information or private content through social media platforms. This could be due to a misunderstanding of privacy settings, accidental posting, or a hack into Jayde’s social media accounts.
- Data Breach: If Jayde is associated with an organization or database, a leak could occur due to a data breach. This might involve hacking, insider threats, or physical theft of data storage devices, leading to the unauthorized release of sensitive information.
- Whistleblowing: In a more intentional scenario, Jayde might have chosen to leak information as a form of whistleblowing. This could involve revealing unethical practices, illegal activities, or crucial information that the public has a right to know, often at personal risk to Jayde.
- PhysicalLeaks: Jayde could have leaked physical documents or devices containing sensitive information. This might happen through loss, theft, or the intentional release of these materials to unauthorized parties.
- Collaboration Errors: If Jayde is involved in collaborative projects or works with others, leaks could occur due to miscommunication, misplaced trust, or the failure to secure shared information properly. This might involve email mishaps, unsecured cloud storage, or other collaboration tool vulnerabilities.
Consequences of Leaks
Leaks, regardless of their nature or intent, can have profound consequences. For Jayde, these might include legal repercussions, damage to reputation, loss of trust among peers or the public, and in severe cases, physical harm. The impact can also extend to associated individuals, organizations, or communities, leading to a ripple effect of consequences.🚨 Note: The consequences of leaks can vary widely depending on the context, nature of the leaked information, and the parties involved.
Mitigating Future Leaks
To prevent future leaks, especially in contexts where Jayde has control or influence, several steps can be taken: - Enhance Security: Implement robust security measures, including encryption, secure storage, and access controls. - Educate: Provide education and training on data privacy, security best practices, and the importance of confidentiality. - Review Policies: Regularly review and update policies related to information sharing, collaboration, and data protection. - Use Secure Tools: Utilize secure communication and collaboration tools that offer end-to-end encryption and other security features. - Conduct Audits: Periodically conduct audits to identify and address potential vulnerabilities.Embedding Images for Illustration
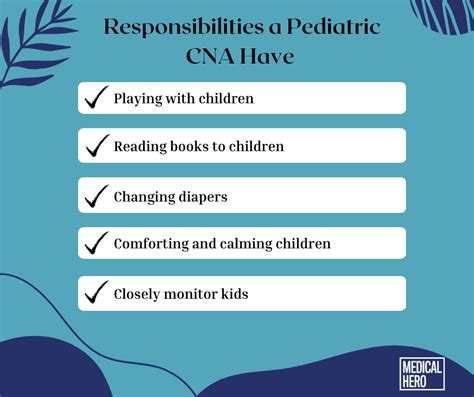
 In the context of preventing leaks, visual aids like the one above can help illustrate the importance of robust security measures, including both digital safeguards and physical security protocols.
In the context of preventing leaks, visual aids like the one above can help illustrate the importance of robust security measures, including both digital safeguards and physical security protocols.
Table of Potential Leak Sources
| Source | Description |
|---|---|
| Social Media | Unauthorized posts or breaches of social media accounts |
| Data Breaches | Hacking, insider threats, or physical data theft |
| Whistleblowing | Intentional release of information for public interest |
| Physical Leaks | Loss, theft, or intentional release of physical documents/devices |
| Collaboration Errors | Miscommunication, misplaced trust, or unsecured shared information |
In conclusion, the concept of Jayde leaking information or content encompasses a broad spectrum of scenarios, each with its own set of consequences and preventive measures. Understanding these scenarios and taking proactive steps towards security and privacy can mitigate the risks associated with leaks.
What are common sources of leaks?
+Common sources of leaks include social media mishaps, data breaches, whistleblowing, physical leaks, and collaboration errors.
How can leaks be prevented?
+Leaks can be prevented by enhancing security, educating individuals on privacy and security, reviewing and updating policies, using secure tools, and conducting regular audits.
What are the consequences of leaks?
+The consequences of leaks can include legal repercussions, damage to reputation, loss of trust, and in severe cases, physical harm, affecting not only the individual involved but also associated parties.